For true security, you need a non-custodial wallet so you own your keys. Protect access with multi-factor authentication and hardware keys. Trust open-source code that’s publicly verified for transparency. Seek advanced privacy via stealth addresses and zk-SNARKs to shield your activity. Finally, ensure you have a solid backup and recovery plan. Discover how these layers create an unbreakable digital fortress for your assets.
Table of Contents
Brief Overview
- Non-custodial wallets give you full control over your private keys and assets, ensuring true ownership.
- Multi-factor authentication and biometrics strengthen access security against unauthorized use.
- Open-source code allows for public verification and audits, building trust through transparency.
- Advanced privacy features like stealth addresses and zk-SNARKs shield your transaction details.
- Secure backup strategies using durable materials and tested processes protect against loss.
Your Keys, Your Coins: The Non-Custodial Foundation
The foundational concept of any secure cryptocurrency wallet is simple: if you don’t control the keys, you don’t own the coins. This is the core promise of a non-custodial wallet: you hold your private keys, granting you full control over your digital assets. You aren’t reliant on a third party, so your security isn’t tied to their vulnerabilities. This direct control enables enhanced privacy for your transactions, as they aren’t linked to a centralized account. For long-term viability in a regulated environment, fostering user trust is vital. A secure non-custodial wallet lets you manage a broad portfolio from one interface. You can further fortify your holdings by implementing measures like biometric authentication, ensuring that access remains exclusively yours.
Locking Down Access: Multi-Factor and Hardware Security
While non-custodial wallets give you direct control, that control must be actively defended. You must layer defenses to protect your private keys. Use multi-factor authentication to block unauthorized access, and consider hardware security keys for a physical additional layer of security. Biometric authentication on many secure wallets further ensures only you can unlock your assets. For ultimate control, multi-signature wallets require multiple approvals for any transaction. This is especially critical given increasing government scrutiny and the regulatory challenges faced by privacy technologies. Choose hardware wallets with strong encryption protocols and commit to installing all firmware updates promptly. This proactive approach patches vulnerabilities and hardens your core holdings against evolving threats.
Verifying Trust Through Open-Source Code
- Independent Verification: You can audit the open source code yourself or rely on community-vetted security audits to confirm no hidden backdoors exist.
- Rapid Security Enhancements: Collective scrutiny from global developers means vulnerabilities are found and fixed quickly, enhancing safety.
- Proven Reputations: Notable open-source wallets build trust through public development and consistent peer review over time. This transparency aligns with the principle of blockchain transparency that underlies secure transaction technologies.
Integrating Privacy: Stealth Addresses and zk-SNARKs
Beyond basic open-source verification, true financial privacy in 2026 requires advanced cryptographic features built directly into the wallet. You can achieve this by integrating stealth addresses and zk-SNARKs. These privacy features generate unique, one-time addresses and allow you to prove transaction validity without revealing any financial information, ensuring strong transaction privacy. This combination provides robust anonymity on the blockchain, making it extremely difficult to trace your activity. For secure wallets, adopting these blockchain applications gives you greater user control and enhanced security against surveillance. You effectively shield your transaction history from external observers, a critical capability in today’s regulated environment. Modern implementations like Monero’s RingCT further conceal transaction amounts for comprehensive privacy.
Planning for the Unexpected: Backup and Recovery Strategies
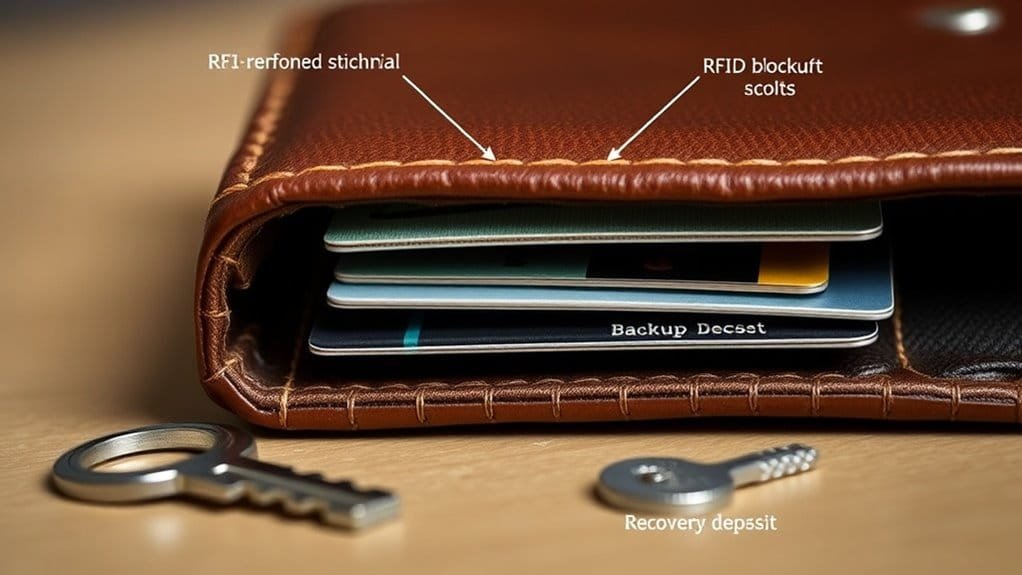
- Store multiple copies of your recovery phrase in geographically separate, secure locations. Use durable materials like steel, not just paper.
- Consider hardware wallets with built-in backup and recovery features for a more resilient and simplified process.
- Regularly test your recovery process to ensure it works. Keep software updated to maintain effective backup methods.
Frequently Asked Questions
Do RFID Blocking Wallets Really Work?
Yes, they work. Real-world tests confirm RFID technology effectiveness. Wallet material types create EMF protection; consumer reviews analyze price versus protection, usability factors, and security advancements across brands for your safety.
What Is the Most Trusted Crypto Wallet?
You protect your assets with a vault-like Ledger or Trezor hardware wallet, prioritizing private key management, cold storage benefits, and wallet security features over software vs. hardware trade-offs.
Can FBI Track BTC Wallet?
Yes, the FBI can trace a Bitcoin wallet because blockchain transparency allows transaction tracing. Your wallet privacy isn’t absolute; law enforcement uses digital forensics to link addresses through patterns in your crypto activity.
Can You Trust Hardware Wallets to Not Steal?
You can trust reputable hardware wallets. They use cold storage and strong encryption, storing your keys offline. Their security hinges on your seed phrase protection and avoiding phishing—keep firmware updated and never share that recovery phrase.
Summarizing
Don’t just secure your assets; secure your future. These features form your digital vault‘s bedrock. But remember, a vault is only as strong as its keeper’s vigilance. Your next transaction, your next connection, could test these very walls. The ecosystem watches, and threats evolve. Choose your wallet with this in mind, because your next move isn’t just a transfer—it’s a statement of your sovereignty in a surveilled age.



